The Same Origin Concern - presenting to W3C [𝕏]
03 Oct 2023Originally posted on X
Last week we presented to @w3c and advocated for some ideas we believe could enhance security for web apps on behalf of @metamask.
Our session (w/ @naugtur) focused on "JavaScript Security".
Mine focused on what we refer to as the "same origin concern".
Here's the gist of it 🧵
But first, FYI, at the bottom post of this thread you’ll find:
1. 🔗 to the full document where we describe our take on the problem, the solution we attempted at, why it fails and what browsers can do to help
2. 🔗 to the recording of the 10m pitch I gave @w3c about this topic
👇🏻
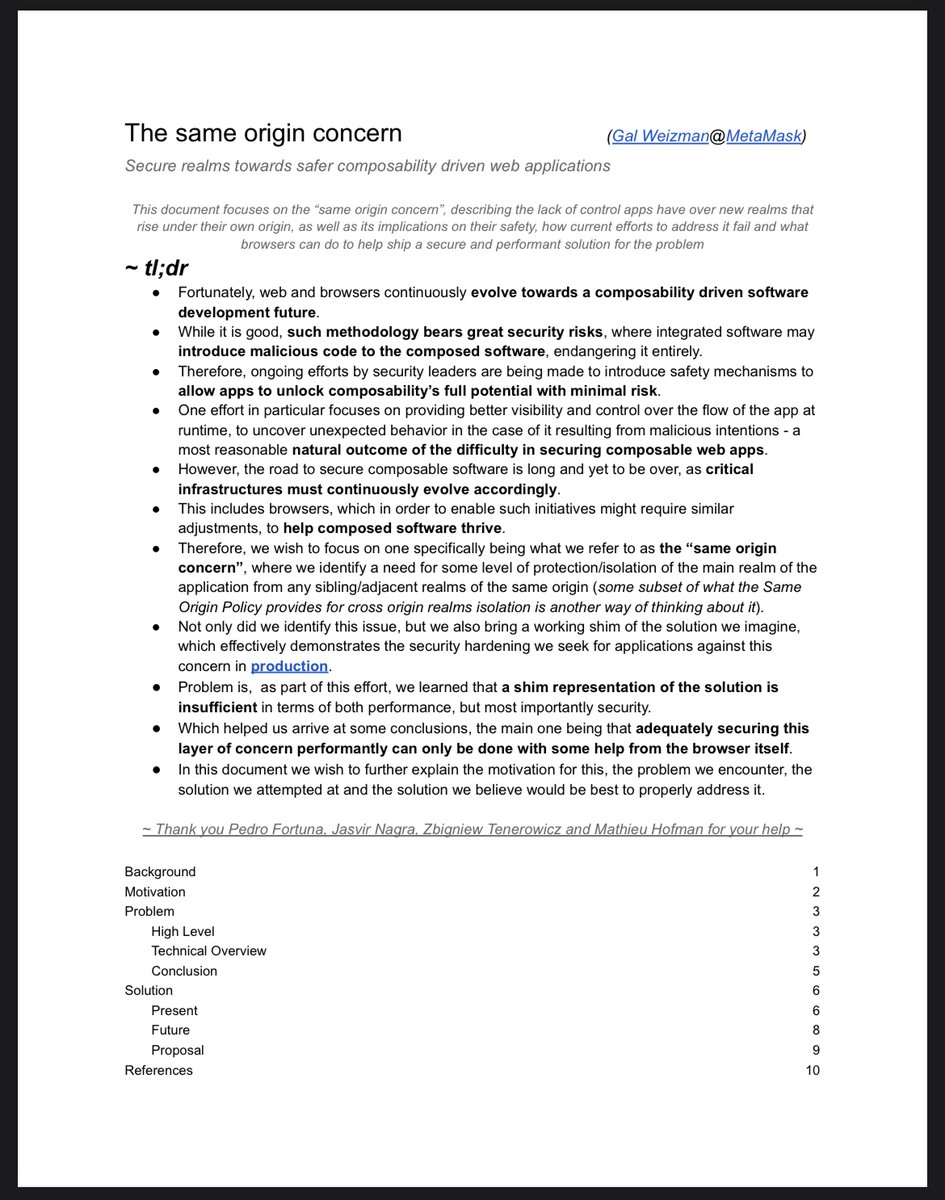
• "Fortunately, web and browsers continuously evolve towards a composability driven software development future
• While it is good, such methodology bears security risks, where integrated software may introduce malicious code to the composed software, endangering it entirely"
• "Therefore, ongoing efforts by security leaders are being made to introduce safety mechanisms to allow apps to unlock composability’s full potential with minimal risk"
• "One effort in particular focuses on providing better visibility & control over the flow of the app at runtime, to uncover unexpected behavior in case of it resulting from malicious actors - a most reasonable natural outcome of the difficulty in securing composable web apps"
• "However, the road to secure composable software is long and not yet over, as critical infrastructures must continue to evolve accordingly
• This includes browsers, which in order to enable such initiatives might require similar adjustments, to help composed software thrive"
• "Therefore, we wish to focus on one specifically being what we refer to as the “same origin concern”, where we identify a need for some level of protection/isolation of the main realm of the application from any sibling/adjacent realms of the same origin (like in SOP)"
• "Not only did we identify this issue, but we also bring a working shim of the solution we imagine, which effectively demonstrates the security hardening we seek for applications against this concern in production"
• "Problem is, as part of this effort, we learned that a shim representation of the solution is insufficient in terms of both performance, but most importantly security"
• "Which helped us arrive at some conclusions, the main one being that adequately securing this layer of concern performantly can only be done with some help from the browser itself"
• "In this document we wish to further explain the motivation for this, the problem we encounter, the solution we attempted at and the solution we believe would be best to properly address it"
For those who are already familiar with my work, we're basically advocating for Snow JS ❄️ to become a native browser feature (kinda).
If you're into security for the web and how browsers can help, please consider reading the full document or watching the 10m pitch I gave @w3c👇🏻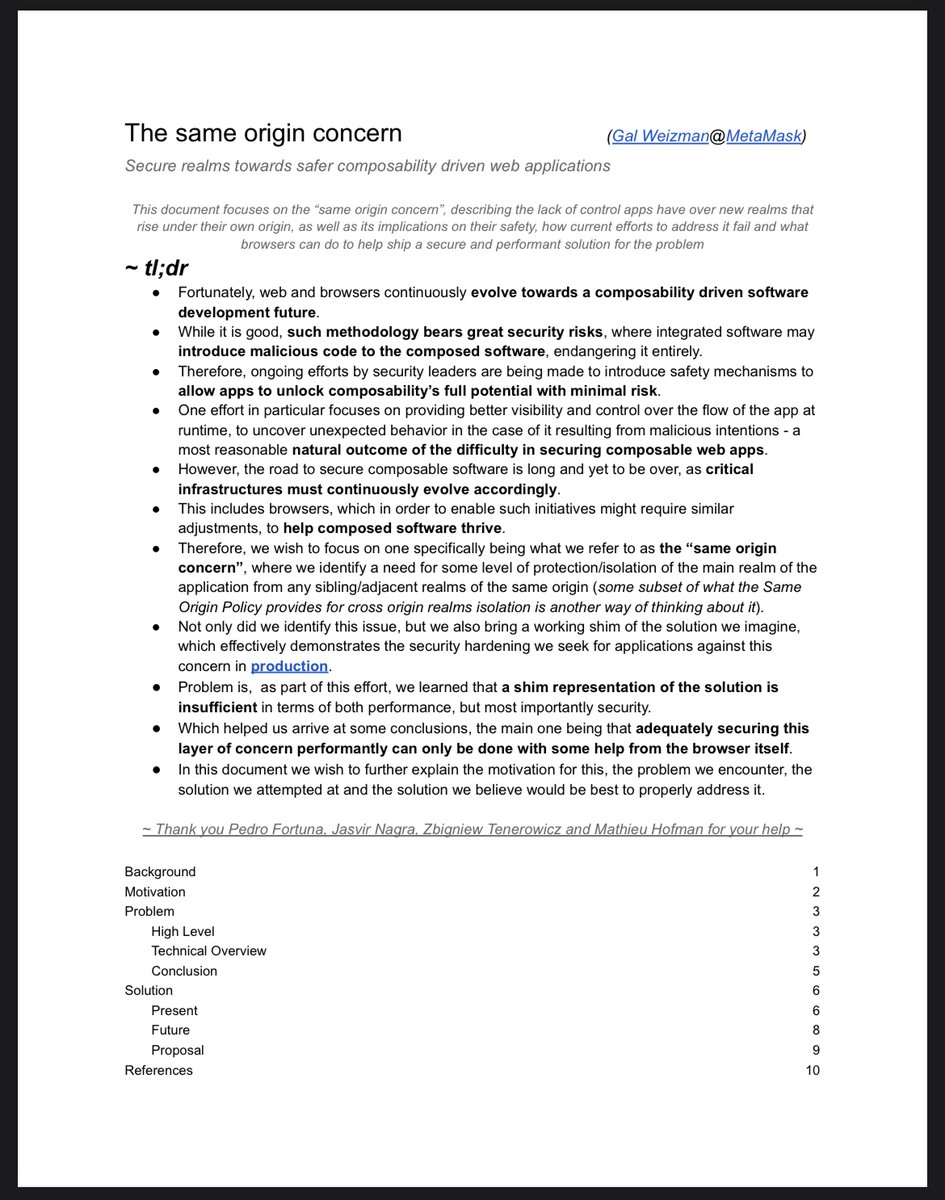
Thanks for all your help @mhofman @naugtur @jasvir @pedrofortunaw3.org/2023/03/secure…
weizmangal.com/content/pdf/Th…
@mhofman @naugtur @jasvir @pedrofortuna Learn more by @w3cdevs:
@mhofman @naugtur @jasvir @pedrofortuna @w3cdevs
Our session (w/ @naugtur) focused on "JavaScript Security".
Mine focused on what we refer to as the "same origin concern".
Here's the gist of it 🧵
But first, FYI, at the bottom post of this thread you’ll find:
1. 🔗 to the full document where we describe our take on the problem, the solution we attempted at, why it fails and what browsers can do to help
2. 🔗 to the recording of the 10m pitch I gave @w3c about this topic
👇🏻
• "Fortunately, web and browsers continuously evolve towards a composability driven software development future
• While it is good, such methodology bears security risks, where integrated software may introduce malicious code to the composed software, endangering it entirely"

• "Therefore, ongoing efforts by security leaders are being made to introduce safety mechanisms to allow apps to unlock composability’s full potential with minimal risk"
• "One effort in particular focuses on providing better visibility & control over the flow of the app at runtime, to uncover unexpected behavior in case of it resulting from malicious actors - a most reasonable natural outcome of the difficulty in securing composable web apps"
• "However, the road to secure composable software is long and not yet over, as critical infrastructures must continue to evolve accordingly
• This includes browsers, which in order to enable such initiatives might require similar adjustments, to help composed software thrive"
• "Therefore, we wish to focus on one specifically being what we refer to as the “same origin concern”, where we identify a need for some level of protection/isolation of the main realm of the application from any sibling/adjacent realms of the same origin (like in SOP)"
• "Not only did we identify this issue, but we also bring a working shim of the solution we imagine, which effectively demonstrates the security hardening we seek for applications against this concern in production"
• "Problem is, as part of this effort, we learned that a shim representation of the solution is insufficient in terms of both performance, but most importantly security"
• "Which helped us arrive at some conclusions, the main one being that adequately securing this layer of concern performantly can only be done with some help from the browser itself"
• "In this document we wish to further explain the motivation for this, the problem we encounter, the solution we attempted at and the solution we believe would be best to properly address it"
For those who are already familiar with my work, we're basically advocating for Snow JS ❄️ to become a native browser feature (kinda).
If you're into security for the web and how browsers can help, please consider reading the full document or watching the 10m pitch I gave @w3c👇🏻
Thanks for all your help @mhofman @naugtur @jasvir @pedrofortunaw3.org/2023/03/secure…
weizmangal.com/content/pdf/Th…
JavaScript realms used to bypass and eliminate web apps security tools - A problem with a WIP solution - Gal Weizman - W3C Secure the Web Forward Workshop
Bringing together experts to drive developer awareness and adoption of Web security standards and practices
https://www.w3.org/2023/03/secure-the-web-forward/talks/realms.html
@mhofman @naugtur @jasvir @pedrofortuna Learn more by @w3cdevs:
@mhofman @naugtur @jasvir @pedrofortuna @w3cdevs
